1000+ Automated Security Posture Optimization Across ZIA and ZPA
Security Checks That Fix Themselves
Scroll Down
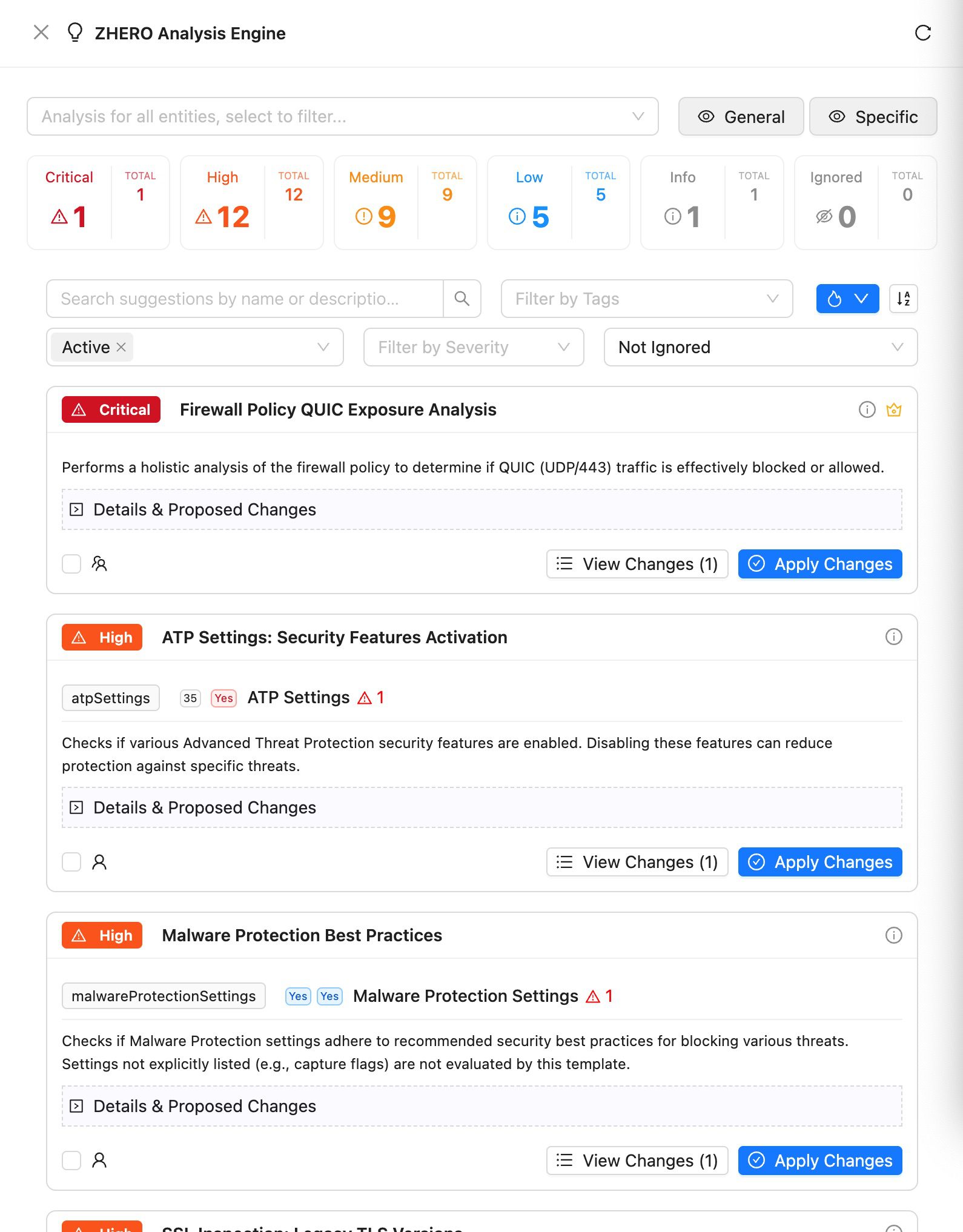
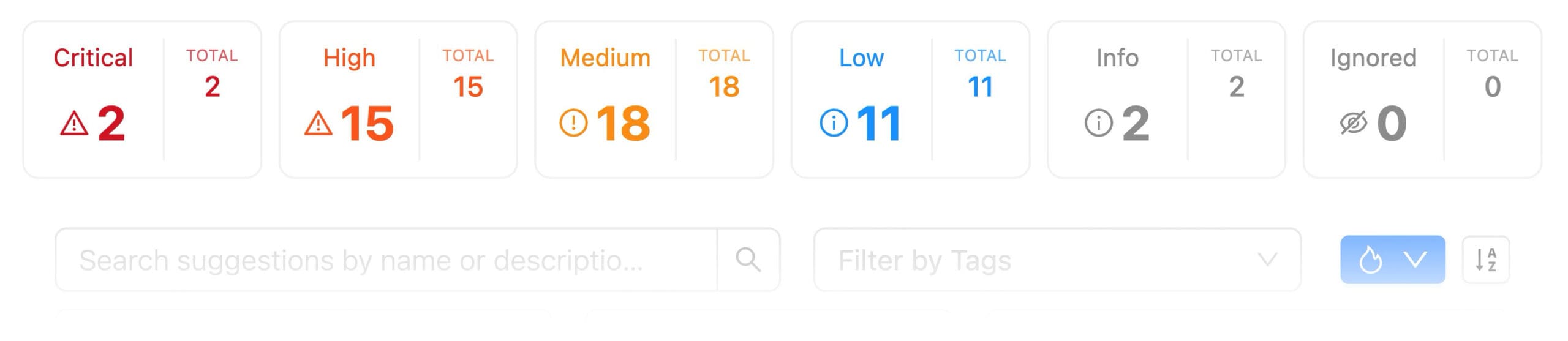
Let ZHERO’s expert analysis engine continuously scan your Zscaler configuration for security gaps, optimization opportunities, and best practice violations — with automatic resolution proposals and one-click remediation for identified issues.
Evergrowing Library ofdivided in categories
Security Posture
- SSL Inspection Bypass Risks: Detect overly broad SSL exemptions that create blind spots
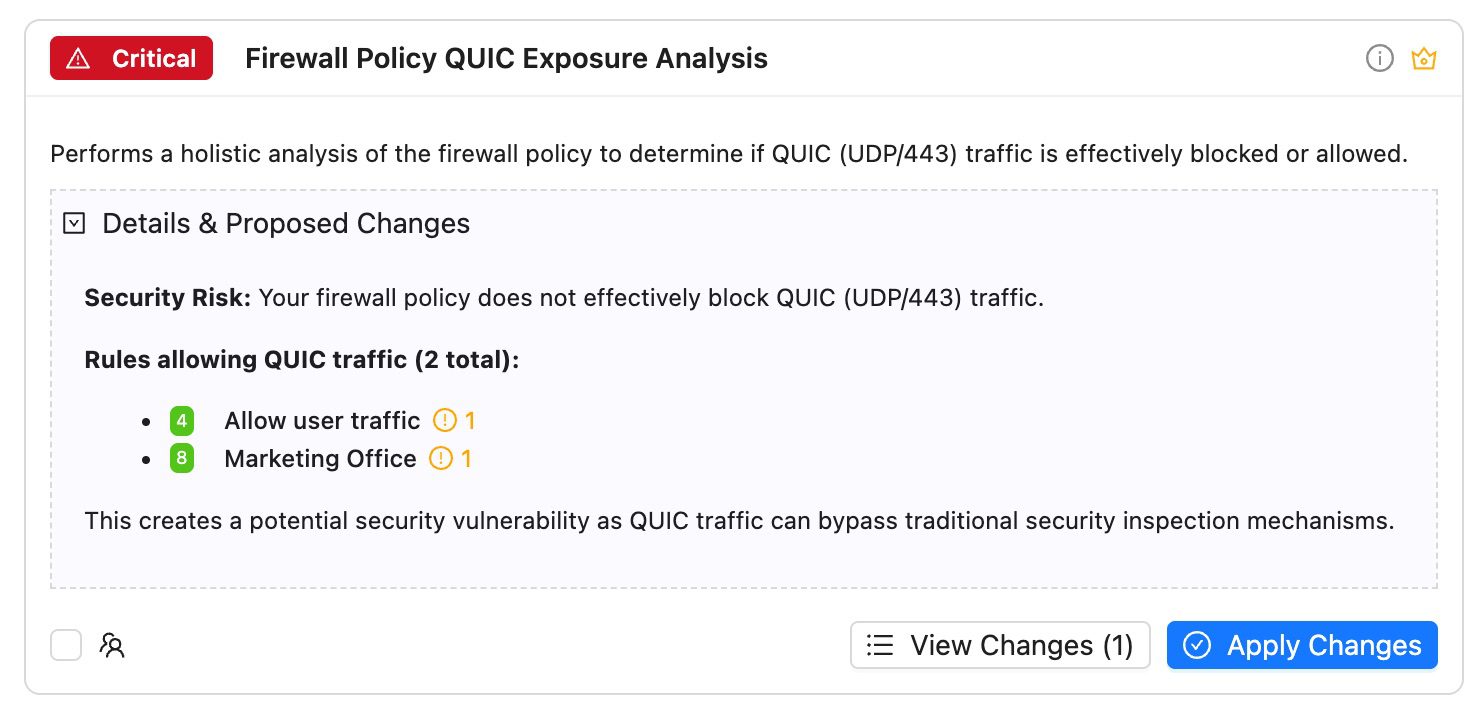
- QUIC Traffic Leaks: Identify firewall rules allowing unencrypted QUIC traffic on both UDP/443 and UDP/80
- Data Protection Holes: Discover unprotected sensitive data paths
- IdP Certificate Expiry Monitoring: Proactive alerts before authentication certificates expire
Optimization
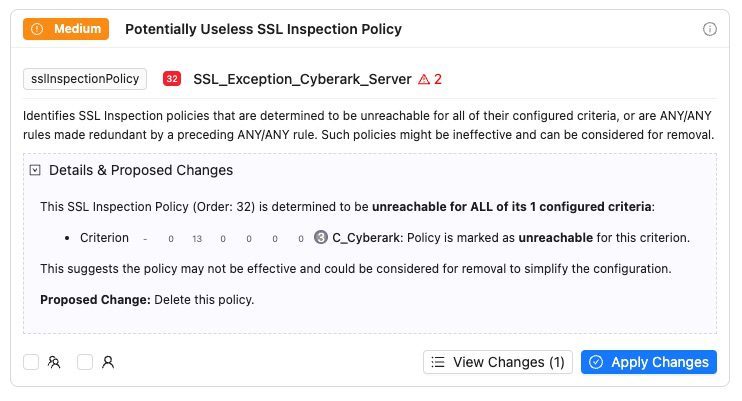
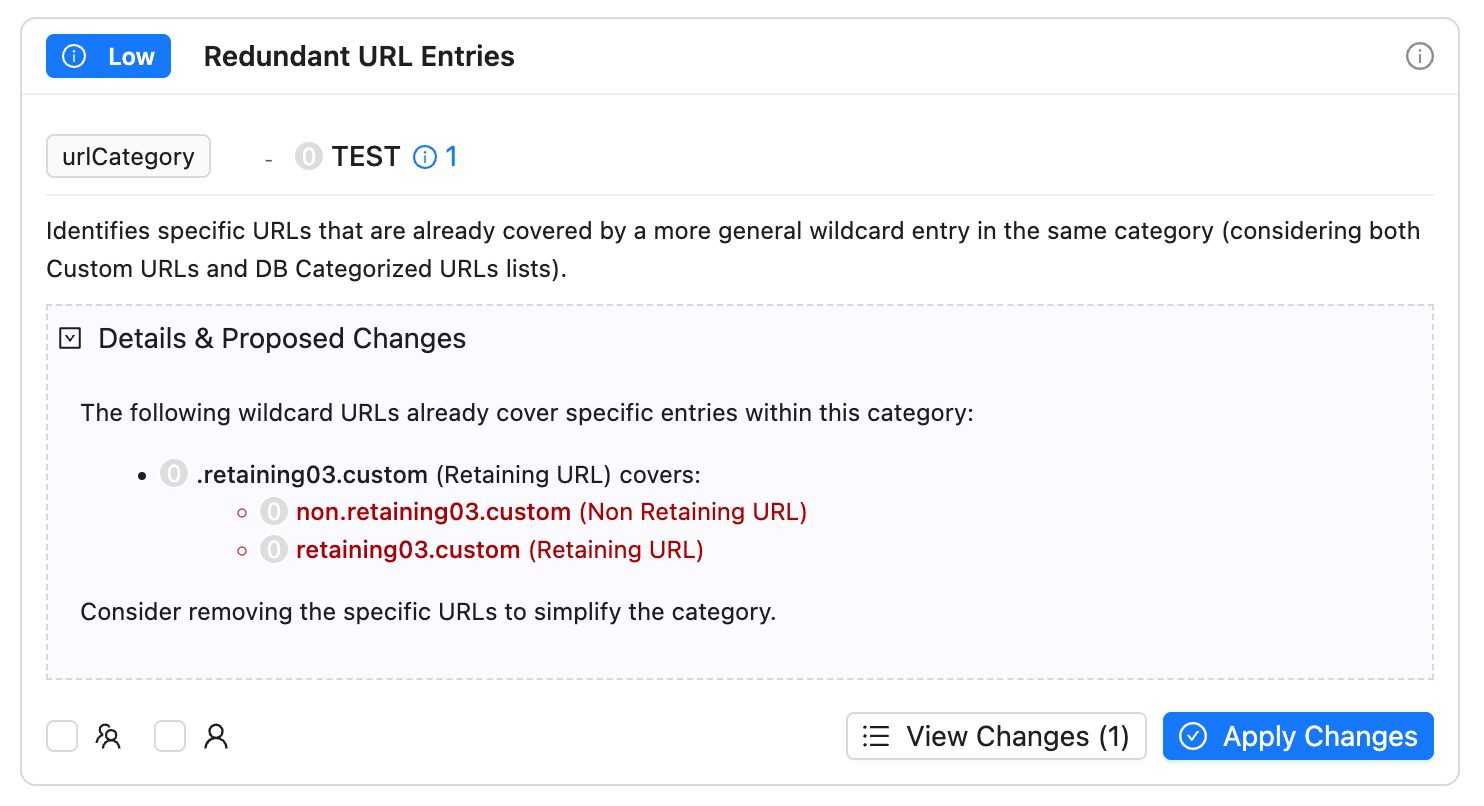
- Redundant Policies/Entities: Identify duplicate or overlapping rules that slow processing
- Unreachable Rules: Detect policies that never get evaluated
- Unused Entities: Find categories, groups, and rules with no traffic in 30+ days
- IP/CIDR Containment Detection: Identify redundant or overlapping IP ranges across rules
Compliance
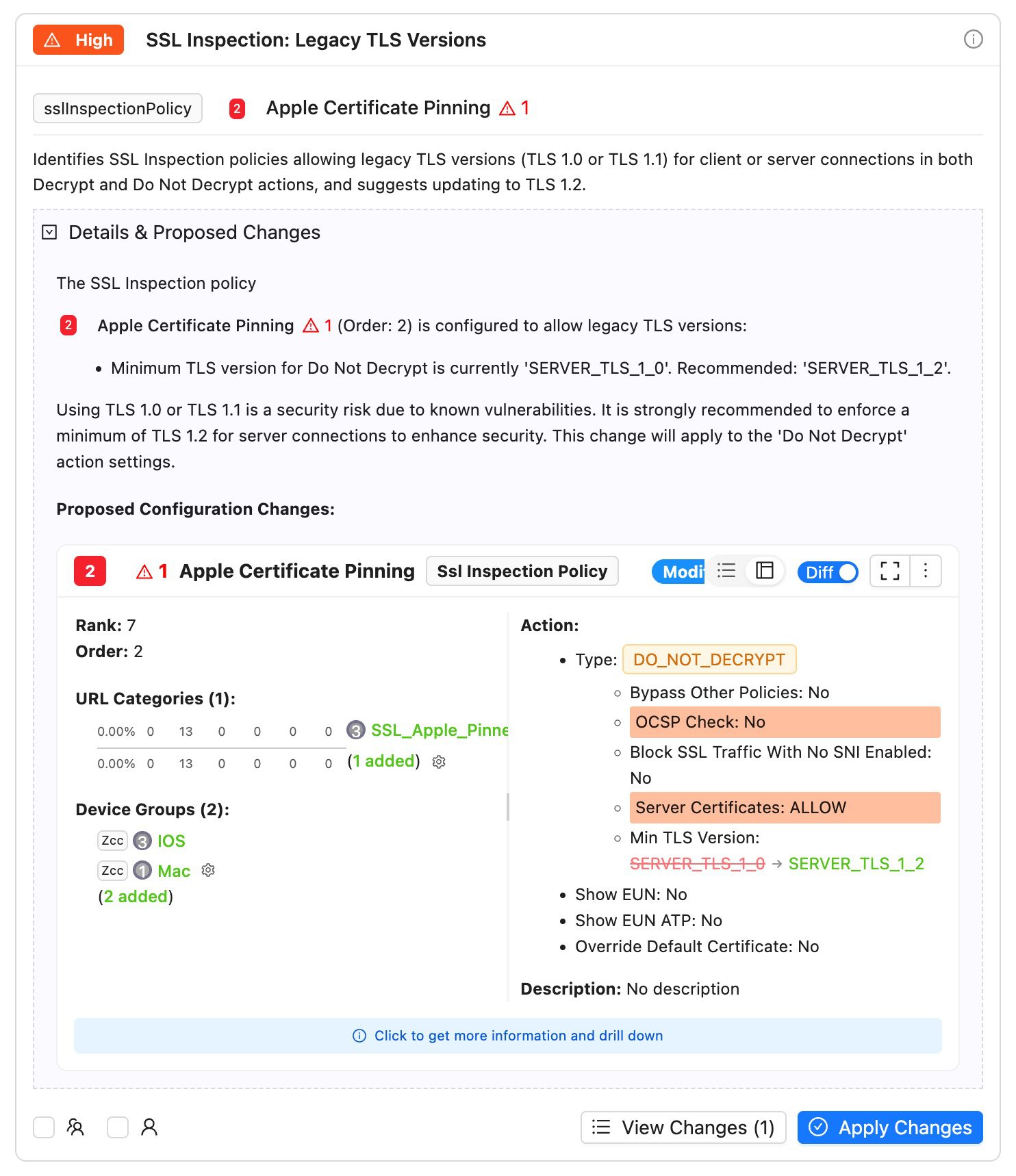
- TLS Version Compliance: Enforce modern encryption standards (TLS 1.2+)
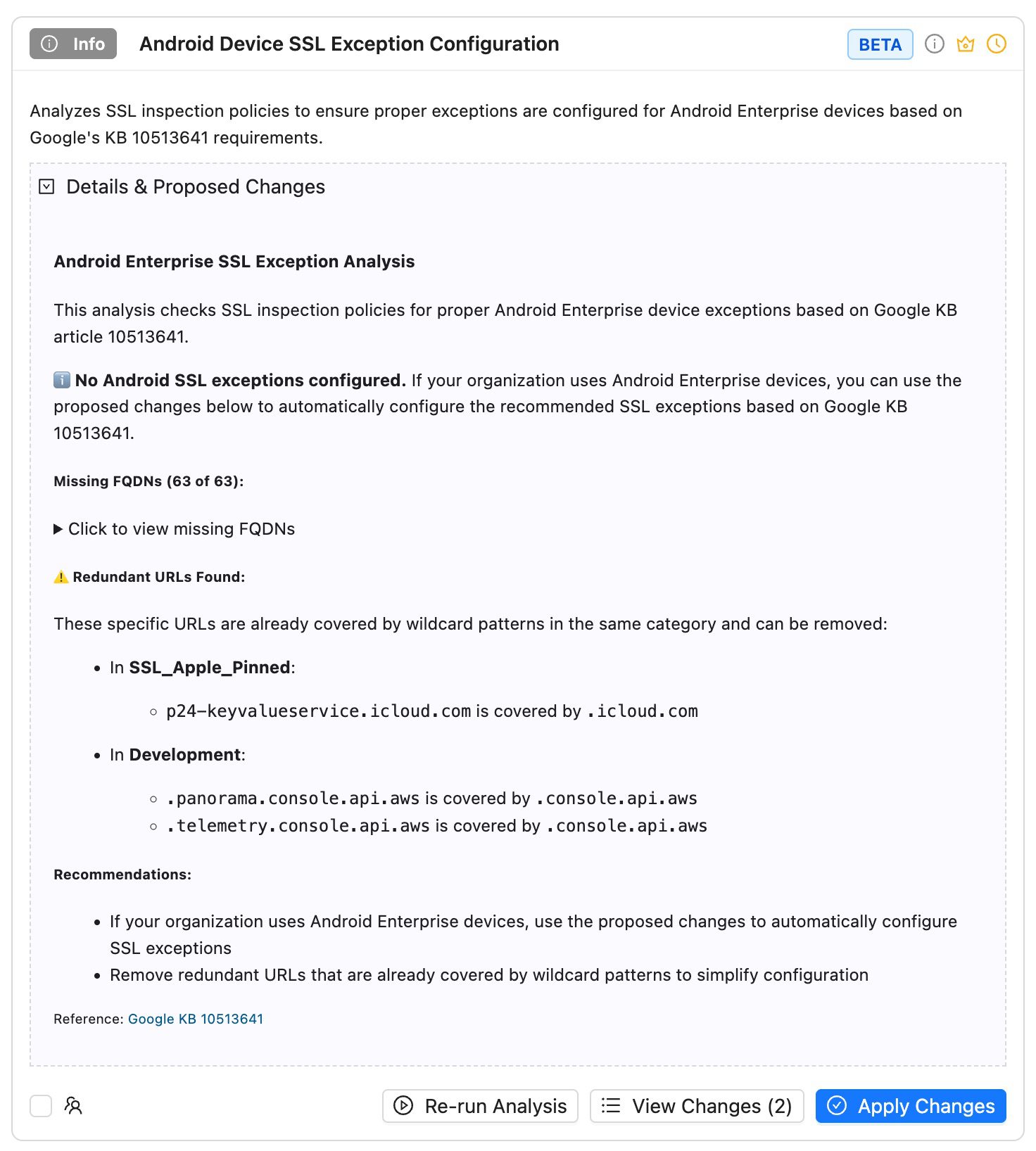
- Device Management Standards: Apple KB 101555, Google KB 10513641 compliance
- Regulatory Alignment & Industry Benchmarks
Best Practices
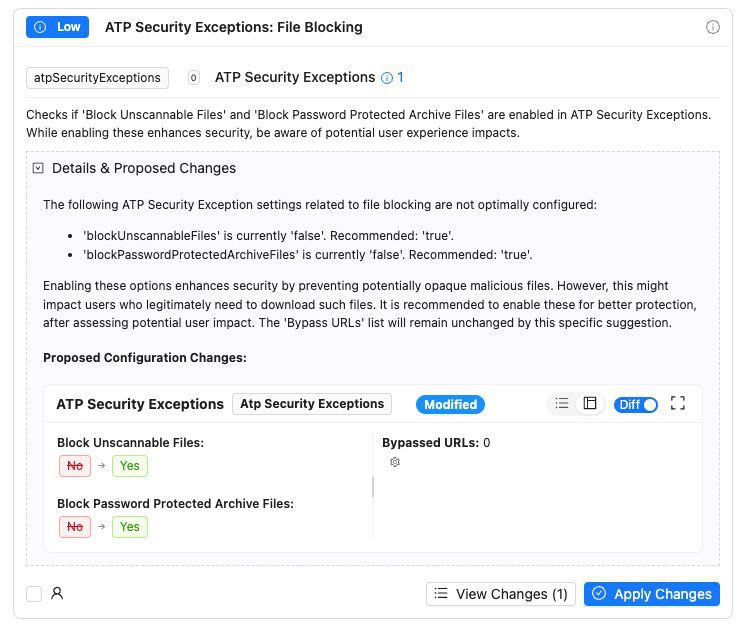
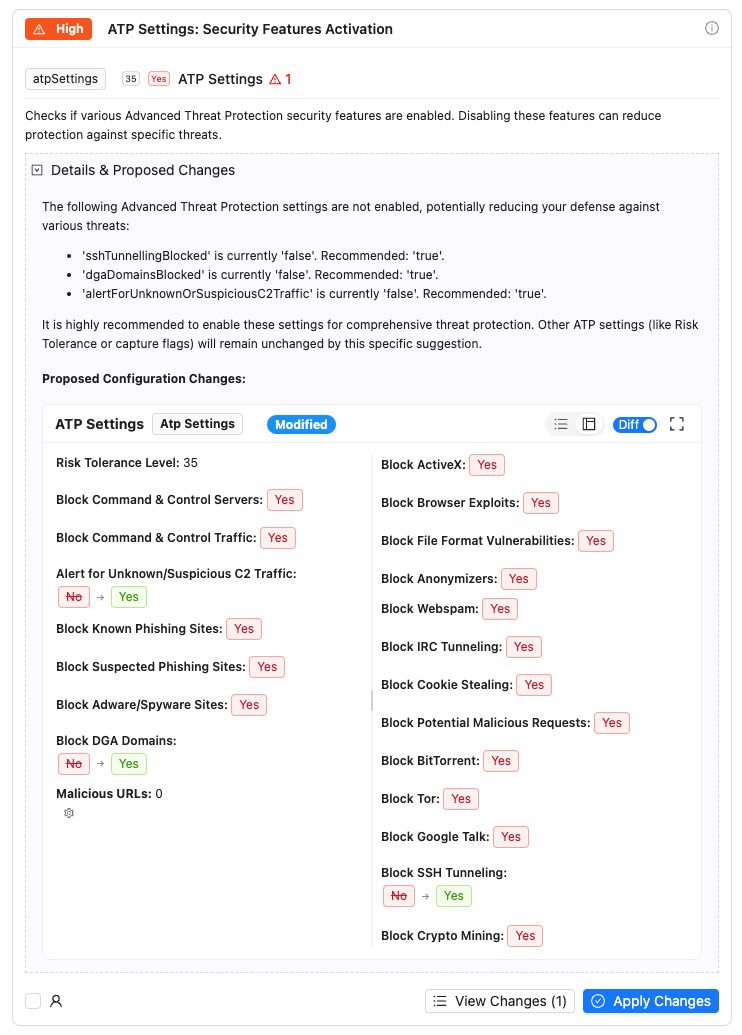
- Malware Protection Settings: Optimal threat prevention configuration
- ATP Risk Tolerance: Balanced security vs. user experience settings
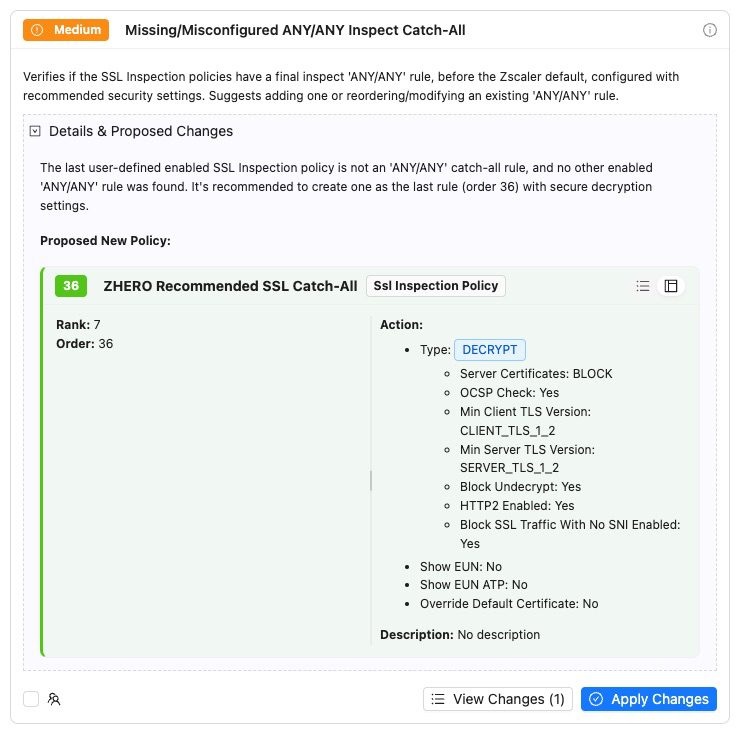
- SSL Catch-All Rules: Proper ANY/ANY rule implementation
- Security Feature Activation: Enable all recommended protection features
Intelligence
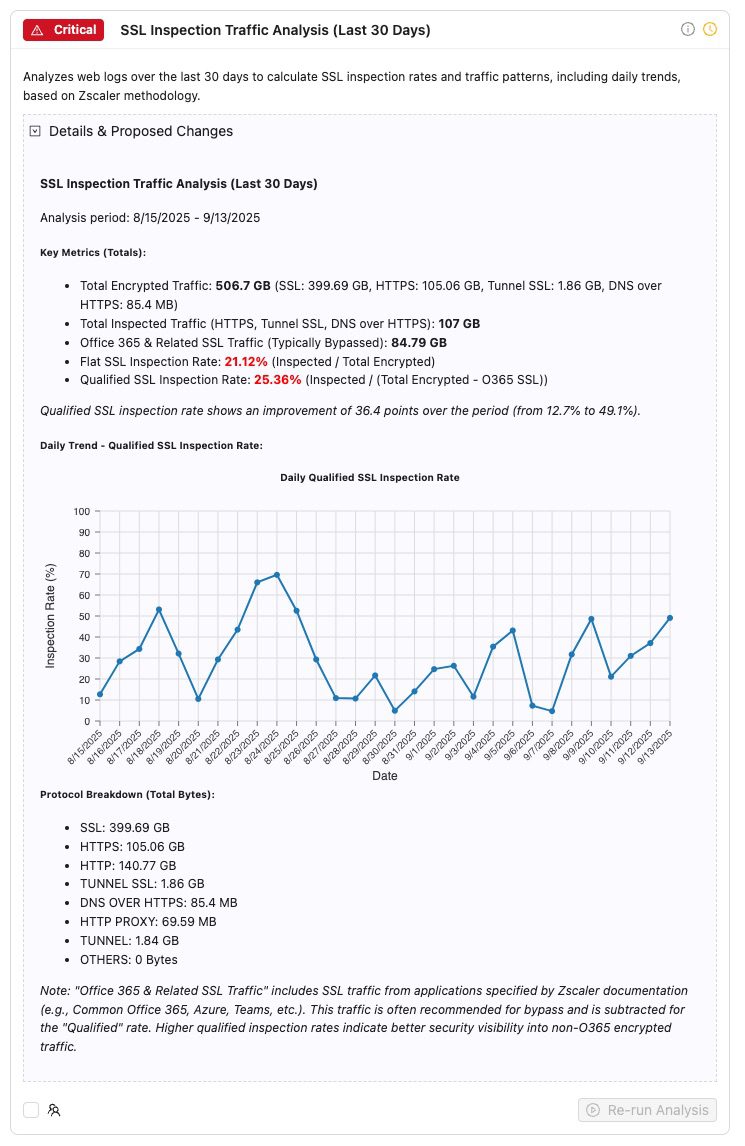
- Traffic Pattern Analysis: 30-day SSL inspection rates and trends
- Behavioral Anomalies: Unusual configuration combinations or access patterns
- Predictive Maintenance: Identify issues before they impact users
- Usage-Based Recommendations: Optimize based on actual traffic data
Core Analysis Categories
Security Posture
Optimization
Compliance
Best Practices
Intelligence
Intelligent Analysis in Three Steps
Want to know more?
The Configuration Complexity Challenge
Zscaler offers hundreds of configuration options, but knowing the optimal settings requires deep expertise and constant vigilance:
ZIA Analysis Templates in Action
A few examples from our growing library of expert-validated ZIA analysis patterns.
Just a few examples of our analysis templates in action:
ZPA Analysis Templates NEW
First-ever analysis templates for ZPA — 14 expert-validated templates that extend ZHERO’s best-practice analysis beyond ZIA, covering access policy security, application segment hygiene, and configuration cleanup.
Access Policy Catch-All
Detect catch-all rules that may bypass intended access controls — overly broad policies that shadow more specific rules below them.