Advanced Reports Generate Comprehensive Zscaler Reports in Seconds
Data-Driven Zscaler Insights
Scroll Down
10+ professional EXCEL export types powered by a unified Export Engine with templates and column customization, traffic analytics and collaboration notes.
Want to know more?
Evergrowing list of
Advanced Export Engine
All exports share a powerful customization engine:
- Export Templates: Save and reuse export configurations per tenant
- Column Selection & Reordering: Choose exactly what data to include and in what order
- Matrix Expansion Mode: Expand multi-value fields into individual rows for deep analysis
- Collaboration Data: Include entity tags and comments in exports
- Consistent Professional Formatting: Headers, filters, freeze panes, and conditional highlighting
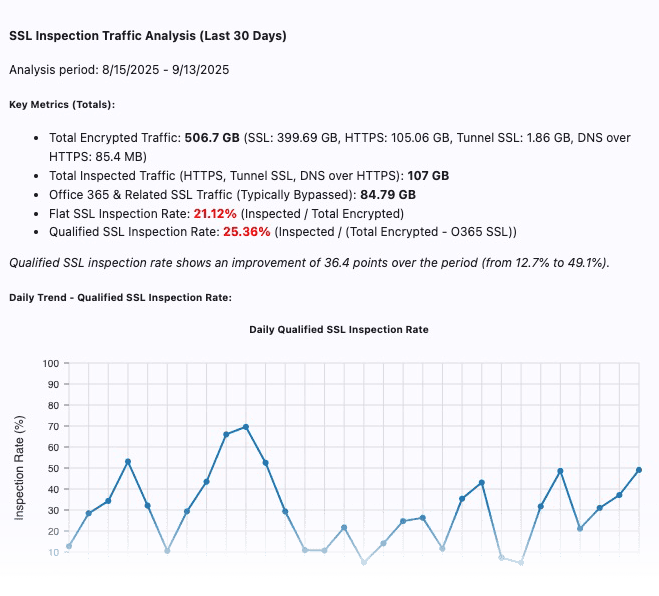
SSL Inspection Analytics
- SSL inspection rate (% of traffic inspected)
- Traffic volume trends over 30 days
- Office 365 and SaaS app inspection rates
- Gap analysis and optimization opportunities
- Identify security blind spots
- Justify inspection policy changes
- Track improvement over time
- Demonstrate compliance
Note: This is generated as part of the Smart Analysis templates feature

URLs Advanced Export
Comprehensive Data:
- All configured URLs with wildcard detection
- Custom category assignments and counts
- URL lookup data with cloud app identification
- Policy impact metrics across all rule types
- Usage tracking in firewall, DNS, forwarding, and IPS rules
- PAC file and App Profile references
- URL relationship mapping (generic/specific patterns)
- Detailed rule usage breakdowns
- Reference tracking across policy types
- Advanced auth bypass and ATP URL detection
- FTP settings integration
Use Cases:
- URL inventory and cleanup projects
- Category optimization and management
- Cloud app discovery and governance
- Policy rationalization initiatives
- Security posture assessment
- Compliance documentation

Location Configuration Report
Complete Location Intelligence
Comprehensive Data:
- All locations and sub-locations
- Configuration settings per location
- Policy usage count for each location
- Traffic volume (last 30 days)
- Location Groups
- Location cleanup projects
- Bandwidth planning
- Policy optimization
- Compliance verification
App & Forwarding Profiles Resport
ZCC Configuration Analysis
Profile Intelligence:
- Complete profile inventory
- Configuration details per profile
- Active usage indicators
- PAC file analysis
- Identify redundant profiles
- Cleanup unused profiles and PAC files
- Standardize configurations
- Simplify management
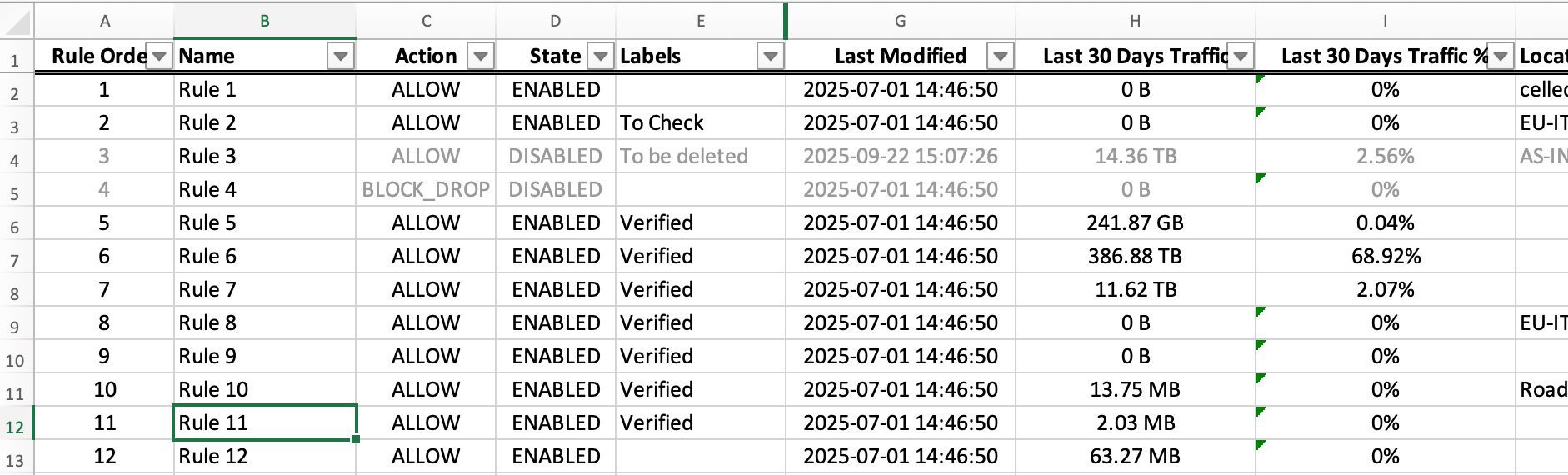
Firewall Rules Export
Complete FW Rules Intelligence
Comprehensive Data:
- All configuration in a sortable/filterable excel
- Configuration settings per rule
- Traffic volume (last 30 days)
- Rule cleanup projects
- Policy optimization
- Compliance verification
SSL Inspection Policy Export
SSL Policy Rules Intelligence
Comprehensive Data:
- Complete SSL inspection policy rules with criteria
- Action types and exception handling
- Category and application assignments
Use Cases:
- SSL inspection coverage assessment
- Policy rationalization
- Compliance documentation
Export Format: Excel with filters and formatting
ZPA Access Policy Export
ZPA Policy Configuration Intelligence
Comprehensive Data:
- Complete ZPA access policy rules with condition
- Flat mode (one row per rule) and expanded mode (one row per condition)
- Policy conditions visualization
- Application segment assignments
Use Cases:
- ZPA policy audits and documentation
- Access review and compliance
- Policy optimization across application segments
Export Format: Excel with flat and expanded sheets
ZPA Application Segment Export
ZPA Application Inventory Intelligence
Comprehensive Data:
- Application segments with domain and server details
- TCP/UDP port configurations
- Segment group assignments
- Health check and bypass settings
Use Cases:
- Application inventory documentation
- Segment optimization and cleanup
- Access architecture review
Export Format: Excel with filters and formatting
URL Filtering Policy Export
URL Policy Configuration Intelligence
Comprehensive Data:
- URL filtering rules with category assignments
- Action types and block/allow decisions
- Protocol and traffic type criteria
Use Cases:
- URL policy audit and documentation
- Category coverage optimization
- Policy cleanup and consolidation
Export Format: Excel with filters and formatting
Cloud App Control Rule Export
Cloud Application Control Intelligence
Comprehensive Data:
- Cloud application control rules and actions
- Application categories and risk levels
- Tenant restrictions and access controls
Use Cases:
- Shadow IT assessment
- Cloud application governance
- Risk-based access control review
Export Format: Excel with filters and formatting
Pending Changes PDF Export
Professional Change Documentation
Report Contents:
- PDF with team context
- Visual entity diff cards showing before/after comparisons
- Complete change summary with author attribution
- Entity type and action categorization
Use Cases:
- Change approval workflows
- Stakeholder review (for team members without ZHERO)
- Audit trail documentation
- Compliance evidence
Export Format: PDF with visual diff cards
Security Posture Report (Coming Soon)
- Configuration metrics summary
- Security gaps identification
- Best practice compliance
- Policy optimizability index
- Overall security score
- Critical findings summary
